The Singapore MICE Forum in Singapore was organized amid the COVID19 pandemic. The event was limited to the one-on-one interaction that would see many business people and organizations come together for the event. The event delivered a keynote address, which concentrated on how activities will grow in the long term. The study will document released by the STB, PCMA, and UFI showed how business executives changed in reaction to the epidemic and provided a worldwide assessment on knowledge gained and possible recovery paths.
Risk assessment is about anticipating what might happen during the development and coordination of an event. It is focused on taking actions to minimize the likelihood of unfortunate consequences emerging or accepting the possibility of something happening and being equipped for the repercussions. Additionally, it focuses on increasing the benefits of an occasion and guaranteeing it is as effective and safe as appropriate. The focus is on event organizers using a systematic methodology to risk assessment to make sound judgments and convey to others that they followed a transparent procedure in reaching those judgments. These judgments frequently include deciding whether or not to embrace inevitable consequences. Additionally, risk management provides event organizers with a comprehensive approach for identifying and managing critical risk vulnerabilities, allowing them to focus their efforts on the areas where they will be particularly successful. Because no organization has enormous resources, prioritizing is critical for successful event organization and execution.
The following event risk management strategy plan was developed for the Singapore MICE forum.
Identifying Event Risk Requirements
In identifying the risk requirements of the event, the function organizers, the Singapore Association of Convention & Exhibition Organizers and Suppliers (SACEOS), had to specify the various anticipated risk that the event was to face. The risk requirements of the event are those incidents or circumstances that, if not adequately handled, can jeopardize the successful creation of an end product. For instance, the various anticipated hazards like the risk of attention and attraction associated with digital technology would impact the event to the point of canceling the function if not adequately addressed.
Discussing the Risks with Project Team
Analyzing the various risks that will be anticipated in the event would help generate various ideas on how to prevent or mitigate the risks. The identified risks include digital technology risks, people risks, and operational risks. While assessing the risks, the following aspects would be taken into consideration. These are the inherent dangers and concerns that will be circumvented. Generally, the variables that can jeopardize the company’s event include safety concerns. Because the event’s planning is a collective task, sharing ideas on the nature of the risks would enable the successful operation of the function.
For instance, people risks include safety risks that include any potential for physical harm to workers, clients, attendees, contractors, producers, and anybody else participating in the event. Because the event is taking place amid the COVID19 pandemic, the safety of the few participants that are to be in attendance is at risk due to the nature of the virus. The likelihood of transmission of the virus between the individuals in attendance will be low as they will be measures and variables to ensure that they are COVID19 free. Additionally, the conference room and equipment will be sanitized, and seats placed at a minimum distance of 2 meters.
Anticipating Possible Obstacles and Setbacks
Communication breakdown within and across teams, sections, and corporations poses a significant threat in the event. Because this event takes place amid the pandemic, only a few individuals will attend, and the other majority will be streaming the program online. However, this lack of communication can result in sensitive data being withheld from those who require it to mitigate the identified risks. Therefore, this might result in problems occurring due to an organization being unaware of potential threats. Additionally, inadequate supervision could be another anticipated setback in the course of the function. Supervision in many aspects is a risk mitigation operation, and it entails providing proactive direction, which involves assessment, assisting, reprimanding, and leading by example. Supervision strengthens training and ensures that tasks are completed correctly.
Engaging with Internal and External Stakeholders
Making the internal and external stakeholders aware of the possible risks would prove vital since their positions and roles in the event would have been recognized. Internal stakeholders like the financial and human resource managers would provide the necessary workforce and resources to mitigate digital technology and people risks. Provision of finances to hire more labor and the best digital service equipment to facilitate the event would be possible when such stakeholders are engaged.
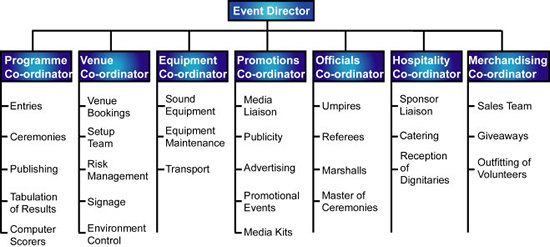
Projecting Team Chart and Assigning Roles & Responsibilities
Establishing a team schedule and ensuring that each member of the project team knows and realizes their duties and functions would enable the successful completion of the event. A project team chart is vital for event risk management as it stipulates the essential components that each event player must undertake in completing the function. The following project team chart will be used for the Singapore MICE Forum.
Devising a Risk Schedule
A risk schedule assists businesses in identifying their vulnerabilities to mitigate their probability and gives a framework for improved decision-making to minimize uncertainties. The Risk Management plan will outline the procedure for evaluating, reviewing, reacting to, tracking, and reporting threats to reduce risk levels to an acceptable limit. It details how risk management actions will be carried out, documented, and assessed throughout the project’s lifecycle and includes procedures for documenting and managing the risks.
Establishing Risk Protocols
Risk protocols define the risk management framework and emphasize the importance of risk identification and risk mitigation in the risk assessment schedule. Although risk management is sometimes depicted as a systematic approach, it is reversible. Risk protocols establish the following: how risk will be identified and the method by which the vulnerability will be controlled. For instance, the risk of attention from the digital technology risk would be monitored by how the various online participants are engaged and follow the proceedings of the event. In controlling the risk, the master of ceremony and the key stakeholders of the meeting will ensure that throughout the event, online participants are actively engaged.
The vulnerability of risk will influence the risk control strategies that one should employ. When developing these plans, planners should not be reluctant to speak with their clients, participants, and colleagues engaged in the function. Risk mitigation strategies are classified into four broad categories, as discussed below.
Risk Avoidance
It entails avoiding risks or scenarios that could result in losses in another way. Additionally, risk avoidance entails abstaining from risky activities. While avoiding risks may appear to be the best course of action, eliminating threats also means foregoing the significant advantage of embracing or keeping the risk. For instance, avoiding a business to minimize the risk of failure also eliminates the chance of profit. In the case of the Singapore MICE event, digital technology risk associated with inattentiveness was the most likely risk that the event was to face. Maintaining the attention of the participants is critical to providing an incredible experience.
While the threat of attention does not have the most significant impact, it does have the most excellent chance. The reason behind this is that most experienced event planners are unfamiliar with the subtleties of online interactions. Keeping an audience’s attention online is challenging. Participants will be contending against a world of finely tailored interruptions every moment of the contest. There will be mails to read, text messages to respond to, and Zoom calls to participate in. The Singapore MICE online meetings will allow audience members to participate and define the material. The Singapore MICE event will be live, the participants will be engaged, and the presentation will be flawless to mitigate this risk.
Risk Retention
Risk-retention means that the party or institution will retain or bear responsibility for losses incurred due to risk exposure. Risk-retention is related to the attitude in which a civilization or organization, whether global or regional, accepts some risk of damage and degradation as a result of regular or unpredictable weather occurrences (Riva, 2020). A case scenario for this strategy is when the event planners decide to retain the digital technology risk of attentiveness. The impact of the risk to the function is that not every participant will be following the event’s proceeds, and thus the aim and objectives of the occasion may not be fulfilled. Online event planning requires keen interest paid on how the attention and monitoring of the participant would be established and made effective. Additionally, the event participants may not be used to attending long-hour conference events online. Thus, this may affect the dissemination of the planned information concerning the event to a limited number of people.
Risk Transfer
Risk Transfer refers to the process through which one party distributes all or a portion of the losses associated with risk vulnerability to another entity for a fee. By exporting the conference to a cloud-based company, we will be transmitting responsibilities such as data integrity and confidentiality to the network operator via an agreement. A case scenario is outsourcing the conference or having an external networking company program the Singapore MICE event. Limited control, miscommunication, unexpected and undisclosed expenditures, worries about confidentiality, and insufficient knowledge working with distributed teams are among the impacts outsourcing of the conference would have on the event. Additionally, vendor non-delivery or persistent setbacks are also anticipated to affect the event.
Risk Reduction
Risk can be managed in two ways: through avoidance or loss control. Avoidance indicates either the minimization of a particular loss exposure or the abandonment of a preexisting one. The main aim of risk reduction for event planners is to avert or mitigate the magnitude of possible losses. The event organizers could develop their networking program to reduce the anticipated losses associated with digital technology risk. Having their internal programming technology managed from within the event’s location would help mitigate outsourcing the conference. Having break sessions in between the event would help increase the concentration span of the participants who will be airing the event online. Because of the many disruptions associated with online conferences, breaks between the meetings would enable individuals to respond to the different distractive agents.
Additionally, the event is to have some individuals being in attendance. Therefore, in reducing the impacts of the social interaction session amid the COVID19 pandemic, the risk management protocols of the virus would be adhered to strictly. Putting on masks at all times, keeping a distance of 2 meters, and sanitizing tables and equipment to be used during the event will all be necessary to mitigate the impacts of the COVID19 implications for the event.
I would use the following decision-making paradigm to ensure that the newly identified risk is under control and reduced impact on the event.
Identifying the Problem Statement
The newly discovered threat addressed to me by one of the team project members was the unstable internet. Since the event depended heavily on the internet to stream the event to participants who could not attend the event in person due to the COVID19 restrictions, the instability of the internet posed a significant risk to the successful completion of the event. The vulnerability was that those attending online would not follow the proceedings of the function entirely. Additionally, they will not be able to make and contribute to the event’s discussion topics.
Collecting Information
The outrage’s assumption could be that the event outsourced the conference to a third-party entity. Therefore, the heavy traffic witnessed by the numerous people using their network could cause instability. The third-party organization that holds the online event, IBTM Wired, has had cases of internet breakdown in the past, particularly when programming events that engage a large number of people. File transfer is one of the primary causes of Internet bottlenecks today (Liu et al., 2018). Users became endpoints in a file-sharing system when programs focused on the BitTorrent specification use their connectivity to transmit information to other consumers while they consume (Liu et al., 2018). Furthermore, because individuals worldwide will be attending the forum, it is normal for some to experience poor internet connections from whichever countries they are from.
Identifying Options
Because of the unstable internet connectivity offered by the IBTM Wired Company, it was essential to look and establish alternatives for the continuity of the event. The available options for me as the event director were to come up with a Zoom meeting link to be shared with all the participants and the cost of internet incurred by us, the event organizers. The Zoom link will be necessary to provide a common platform for the individuals to participate in the function. Having an alternative internet provider on standby (SingTel) in case of such uncertainties would help reduce the chances of unsuccessful events. SingTel is a Singapore-based internet service provider that offers reliable internet connectivity to individuals subscribed to it.
Evaluating Options
The available options, creating a Zoom link and having an alternative internet provider on waiting, seem suitable. However, in deciding what alternative to use, it is prudent to consider the benefits and limitations of using either. Creating a Zoom link to be shared seems suitable and less expensive, but again, it would put the meeting at a standstill for some hours so that participants can switch to the new meeting room. Additionally, some participants may leave the forum for good, never to return because of the disturbance. On the other hand, having a separate internet provider at bay in case of such uncertainties would help significantly. Now that the current internet being used is not stable switching to the other network will not cause a significant issue since movement will take less time. SingTel’s network bandwidth covers a large spectrum and thus would also serve as a viable solution.
Selecting the Best Option
Evaluating the two viable options proved worthwhile by having an alternative internet provider at bay (SingTel). The reasons for selecting the alternative lie solely because switching from the other unstable network to the newly suggested one will take limited time and, therefore, will not significantly impact the business event. Additionally, the cost of shifting from one network to another will be less high and manageable as opposed to creating a Zoom link.
Implementing Action
The selected option, SingTel, having an alternative internet provider at bay, would be done by switching from the IBTM Wired Company’s internet connectivity to the new internet provider. SingTel’s network bandwidth covers a large spectrum and thus would also serve as a viable solution. The operations department tasked with managing the whole activities of the event will be charged with the movement to SingTel. Furthermore, they will ensure that the effect of the transition is less felt among the participants to reduce suspicious activities among the various stakeholders.
Reviewing the Outcome
The aftermath of the movement saw speedy and smooth occurrences of events at the function. The instability of the internet that slowed down the functions’ activities was not witnessed at any point after the internet connectivity was switched to SingTel. At some point, the Master of Ceremony (MD) appreciated the effectiveness of the internet. Additionally, from the transition of events, it was inevitable that everyone, including the participants, was satisfied with SingTel Communication Company’s services.
References
Liu, J., Zhang, C., & Fang, Y. (2018). Epic: A differential privacy framework to defend smart homes against internet traffic analysis. IEEE Internet of Things Journal, 5(2), 1206-1217. Web.
Riva, A. (2020). Risk/return/retention efficient frontier discovery through evolutionary optimization for non-life insurance portfolio. Journal of Applied Finance and Banking, 10(4), 127-156. Web.

